Exploiting Amazon SES for Phishing
Amazon's trusted email platform is now a favored tool for cybercriminals,
enabling phishing campaigns to slip past conventional defenses with ease.
By exploiting exposed AWS access keys found in public repositories,
attackers are orchestrating a surge in malicious email operations.
These messages successfully pass authentication protocols,
as they originate from a legitimate and reputable service.
Security analysts highlight a marked increase in such tactics,
where embedded links direct unsuspecting users to fraudulent websites.
Researchers have identified a growing trend of cybercriminals exploiting Amazon Simple Email Service (Amazon SES) to conduct sophisticated phishing campaigns, with the abuse largely fueled by the widespread exposure of AWS credentials across various online sources.
Exposed AWS access keys are commonly found in GitHub repositories, environment configuration files (.env), Docker images, system backups, and publicly accessible Amazon S3 buckets. Threat actors leverage automated tools — particularly bots built on the open-source TruffleHog utility — to efficiently scan and identify these leaked credentials at scale.
Once valid credentials are discovered, attackers follow a streamlined attack chain: verifying the access key's permissions, confirming email sending limits, and then launching large-scale phishing operations through Amazon SES. According to findings published by Kaspersky, this level of automation has enabled cybercriminals to distribute phishing messages at an unprecedented volume.
What makes these campaigns particularly dangerous is the high quality of the phishing content itself. Attackers craft custom HTML email templates designed to convincingly impersonate legitimate services, complete with realistic login flows intended to deceive even cautious recipients.
Among the attack scenarios observed, threat actors have been found mimicking DocuSign document-signing notifications, redirecting victims to fraudulent pages hosted on AWS infrastructure. More elaborate schemes involve Business Email Compromise (BEC) tactics, where attackers fabricate entire email thread histories to add credibility to their messages.
Finance departments appear to be a prime target, with criminals sending counterfeit invoices in an attempt to manipulate employees into authorizing fraudulent payments — a tactic that continues to cause significant financial harm to organizations worldwide.
Cybercriminals exploiting Amazon SES have found an effective way to bypass standard email authentication mechanisms, including SPF, DKIM, and DMARC protocols, making their phishing campaigns significantly harder to detect and block.
The challenge of mitigation is further complicated by the fact that simply blacklisting IP addresses responsible for delivering these malicious emails is not a viable option, as doing so would disrupt the flow of all legitimate emails passing through the Amazon SES infrastructure.
It is worth noting that Amazon SES is not the only platform being targeted by malicious actors. Cybercriminals are continuously exploring methods to exploit other trusted and widely-used email service platforms as a means to distribute phishing content more effectively.
To counter these threats, Kaspersky has put forward several key recommendations for organizations. These include implementing IAM permissions that adhere to the "least privilege" principle, enforcing multi-factor authentication across accounts, conducting regular key rotations, and establishing IP-based access controls along with robust encryption measures.
When approached for comment, Amazon directed attention to their existing security documentation covering exposed credentials and unauthorized account access prevention. A representative from AWS also confirmed to BleepingComputer that individuals who identify any misuse of AWS infrastructure can submit reports directly through the AWS Trust & Safety channel.
"If anyone suspects that AWS resources are being used for abusive activity, they can report it to AWS Trust & Safety," the AWS spokesperson confirmed.
Editorial note: This article was updated on May 4th at 16:59 EST to incorporate a statement from Amazon that was provided following the original publication.
Emerging Digital Threats
The landscape of digital threats evolves with alarming speed,
as attackers now chain multiple vulnerabilities into single, potent payloads.
These sophisticated maneuvers bypass layered security measures,
including both application and operating system sandboxes.
A surge of advanced exploits looms on the horizon,
demanding a proactive and intelligent defense strategy.
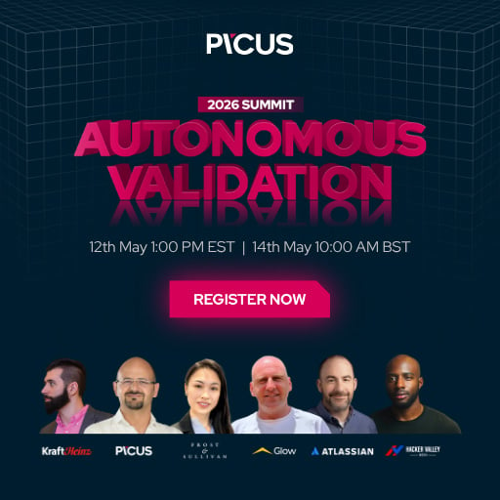
At the upcoming Autonomous Validation Summit,
discover how autonomous, context-rich security validation pinpoints exploitable weaknesses.
This approach verifies that defensive controls remain effective
and ensures a complete, closed-loop remediation process.
Secure your place to stay ahead of these emerging challenges.
Why People Need VPN Services to Unblock Porn
People need VPN services to unblock porn mainly to bypass geo-restrictions and maintain their privacy while browsing. Porn unblocked refers to accessing adult content that is typically restricted in certain regions, and a VPN enables users to do this safely and securely. By masking their IP addresses, individuals can freely explore a wider array of adult sites without compromising their online anonymity or facing potential bandwidth throttling by their ISP.
Why Choose SafeShell VPN to Access Adult Content
If you want to access region-restricted content of Porn by unblocking porn sites, you may want to consider the SafeShell VPN. The benefits of using this service are substantial.
- It provides robust encryption to ensure your browsing activity remains completely private and secure from any monitoring.
- The service offers high-speed connections specifically optimized for streaming, eliminating frustrating buffering when accessing content.
- With its extensive global server network, SafeShell VPN effectively allows you to unblock porn sites that are geographically restricted in your location.
- The VPN supports multiple device connections simultaneously, ensuring protection on your phone, computer, and other gadgets.
- It features user-friendly applications that make it simple to connect and start browsing anonymously within moments.
How to Use SafeShell VPN to Unlock Porn Sites
To begin accessing adult content from any region using SafeShell VPN, you will first need to visit the official SafeShell VPN website and select a subscription plan that suits your requirements. Once you have completed the registration process, proceed to download and install the SafeShell VPN application on your preferred device, whether it be a smartphone, tablet, or computer. After installation, launch the application and navigate to the settings to activate App Mode, which provides enhanced flexibility and broader access capabilities for streaming content from various geographical locations.
With SafeShell VPN properly configured, the next step is to browse through the extensive global server network and choose a server located in the region whose content you wish to access. Simply click the connect button, and within moments, SafeShell VPN will establish a secure, encrypted connection that masks your real IP address and replaces it with one from your chosen region. Once connected, open your preferred browser or streaming application and freely explore adult content from that specific region without any restrictions. Throughout the entire session, SafeShell VPN ensures that your personal identity and browsing activity remain completely private and protected, giving you a worry-free and unrestricted viewing experience from anywhere in the world.