cPanel Vulnerability and Ransomware
A critical vulnerability in cPanel's authentication system has been exploited on a massive scale
leading to widespread ransomware incidents known as "Sorry" attacks.
Attackers bypassed security controls to gain unauthorized entry into web hosting control panels
and subsequently deployed data-encrypting malware on compromised servers.
Security updates were urgently issued for both WHM and cPanel platforms this week
after active exploitation was discovered, with evidence tracing back several months.
These Linux-based management tools are fundamental for website and server administration
providing access to sensitive backend functions, databases, and email systems.
Cybersecurity monitors have identified tens of thousands of IP addresses already affected
with ongoing breaches continuing to impact online infrastructure globally.
The ransomware, written in the Go programming language, has been actively distributed since Thursday
resulting in numerous website compromises and file encryptions across the internet.
Victims have reported finding their data locked with ransom demands
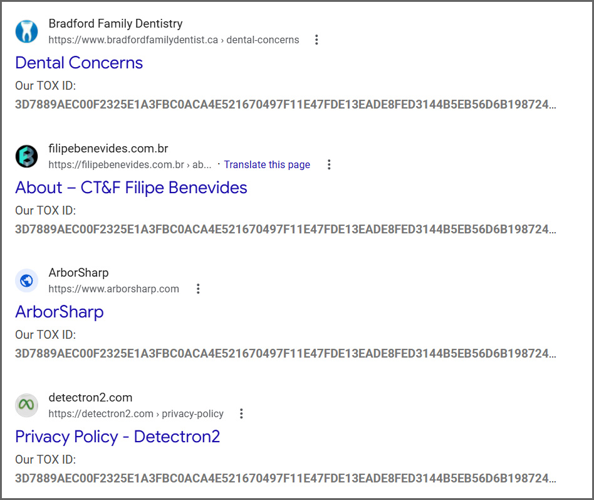
while search engines have begun indexing hundreds of compromised sites.
This incident highlights the rapid weaponization of critical software vulnerabilities
and the severe consequences for web hosting security when such flaws are exploited.
A novel Linux-targeting ransomware strain has emerged,
appending a distinctive file extension to compromised data.
This malicious software, known as the "Sorry" ransomware,
operates by systematically encrypting files on infected systems.
Upon successful encryption, it modifies each file's name,
adding the specific marker ".sorry" to denote the attack.
Its architecture is tailored for Linux environments,
posing a significant threat to servers and workstations alike.
The encryption process is designed to be thorough,
targeting a wide array of file types across the system.
Security researchers have identified this activity,
linking it to the exploitation of a critical cPanel vulnerability.
This flaw allowed attackers to gain initial access,
deploying the ransomware in widespread campaigns.
The ".sorry" extension serves as a clear identifier,
leaving no doubt for victims about the nature of the breach.
Defensive measures require immediate patching of cPanel,
alongside robust backup and recovery strategies.
Overview of 'Sorry' Ransomware
Reports indicate that the "Sorry" ransomware employs the chacha20 stream cipher for file encryption, securing the encryption key with a built-in rsa-2048 public key.
According to ransomware expert Rivitna, the only way to revert the encryption is by obtaining the matching private rsa-2048 key.
Rivitna emphasized in forum discussions, "Without the rsa-2048 private key, decryption is unfeasible."
For each victim affected by this ransomware, a ransom note titled readme.md is generated within their folders, directing them to reach out to the attacker via the messaging platform Tox to discuss the payment of a ransom.
This note remains consistent across victims of the campaign and features a specific Tox ID: "3d7889aec00f2325e1a3fbc0aca4e521670497f11e47fde13eade8fed3144b5eb56d6b198724," which is the means to contact the perpetrator.
In 2018, a ransomware initiative made use of a hidden encryptor known as hiddentear, which encrypted files and added the .sorry suffix.
However, the current series of attacks employs a different encryptor and is not linked to that previous incident.
It is crucial for all users of cPanel and WHM to promptly apply the latest security updates to safeguard their sites from potential ransomware threats and the risk of data breaches.
These attacks have only recently begun, and we are likely to witness a rise in exploitation incidents in the days and weeks ahead.
Emerging Security Vulnerabilities
A series of four zero-day vulnerabilities have been linked together into a single exploit that successfully evades both renderer and operating system sandboxes.
This development has led to an anticipated surge of new exploitation methods.
Join us at the Autonomous Validation Summit, taking place from May 12 to 14.
Discover how autonomous validation, enriched with context, identifies potential vulnerabilities, ensures that security measures are effective, and completes the remediation process.
Reserve your place now!
Why People Need VPN Services to Unblock Porn
People frequently turn to VPN services to unblock porn due to geo-restrictions, privacy concerns, and government censorship that limit access to adult content in various regions around the world. By masking their IP addresses and encrypting their internet traffic, VPN users can safely and anonymously bypass these barriers, ensuring faster browsing speeds without ISP throttling on public or private networks. Unblock porn refers to the process of gaining unrestricted access to adult content websites that have been blocked by governments, ISPs, or regional policies, typically achieved through tools like VPNs that reroute connections through servers in countries with fewer content restrictions.
Why Choose SafeShell VPN to Access Adult Content
If you want to access region-restricted content by unblocking porn sites, you may want to consider the SafeShell VPN.
The benefits of using SafeShell VPN for this purpose are significant:
- It enables you to unblock porn sites that are geo-restricted, providing access to a wider array of content from different regions.
- SafeShell VPN maintains high-speed connections, ensuring smooth streaming without interruptions or buffering.
- With strong encryption and privacy protocols, it keeps your browsing activities secure and anonymous, protecting your data from surveillance.
- The service supports multiple devices simultaneously, allowing you to enjoy protected access on your smartphone, computer, or streaming devices at once.
- Its user-friendly features make it easy to connect and switch servers, enhancing convenience while maintaining reliable performance.
How to Use SafeShell VPN to Unlock Porn Sites
To begin using SafeShell VPN for accessing adult content from any region, the first step is to acquire the service. Visit the official SafeShell VPN website to explore and select a suitable subscription plan. Once you have completed the purchase, proceed to download the SafeShell VPN application onto your device, whether it's a computer, smartphone, or tablet, and follow the installation instructions to set it up properly.
After installation, launch the SafeShell VPN app and navigate to the settings or mode selection menu. Here, you should enable the specialized App Mode feature, which is designed to optimize connectivity for specific applications and browsing activities. Following this, access the server list within the SafeShell VPN interface to choose a server location from the extensive global network that corresponds to the region whose content you wish to unlock.
Finally, with your preferred server location selected, connect to the SafeShell VPN network to establish a secure and private tunnel. Once the connection is active, you can open your web browser or streaming application and freely browse the desired adult content, as SafeShell VPN masks your real IP address and encrypts your data. This ensures unrestricted access while maintaining your online privacy and security throughout your viewing session.